Aunque el proyecto PROMETEO finalizó hace ya dos años, hoy hemos recibido una gran noticia referente a su difusión. Ha sido aceptado un artículo sobre el sistema desarrollado, titulado Forest Monitoring and Wildland Early Fire Detection by a Hierarchical Wireless Sensor Network, en la revista Journal of Sensors, con índice de impacto 1,182. Este artículo describe de forma detallada la red terrena de sensores desarrollada, así como las pruebas que se realizaron durante el transcurso del proyecto.
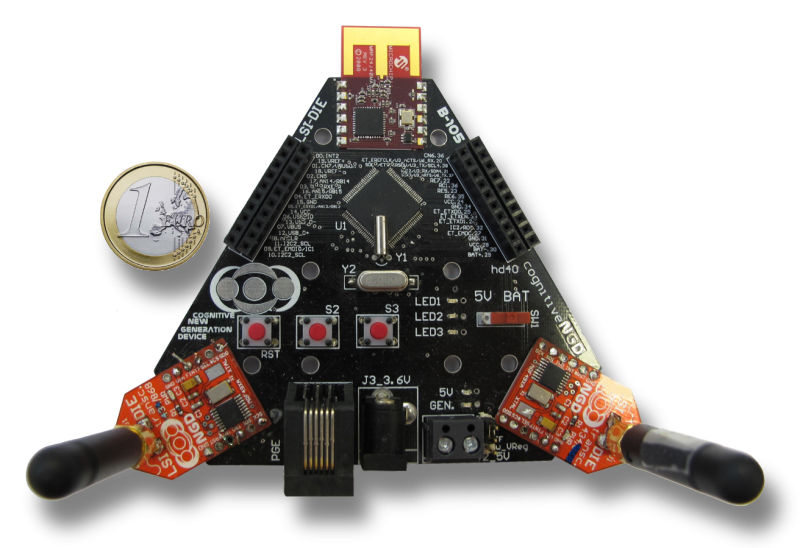
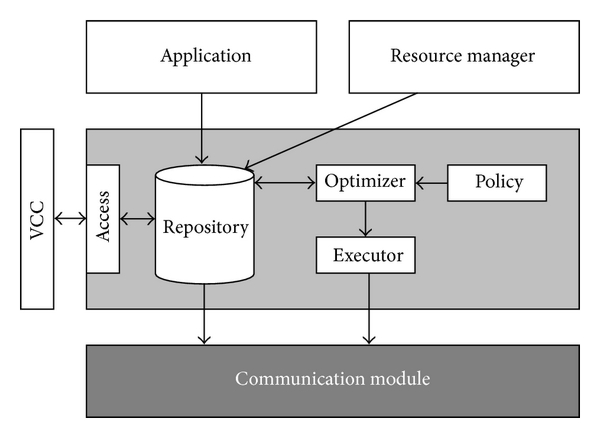
Esta red era el objetivo principal de la tarea en la que participaba el grupo B105 junto al grupo GIICA del Instituto de Tecnología Informática de la Universidad Politécnica de Valencia y la empresa ISDEFE. El grupo B105 se encargó del desarrollo de los nodos finales, encargados de monitorizar la temperatura, humedad y condiciones de viento en el bosque. Estos datos se enviaban inalámbricamente a los nodos centrales, desarrollados por el grupo de la UPV, que los agrupaban y reenviaban al centro de control. La tarea de ISDEFE consistió en la supervisión y seguimiento del proyecto.
En lo que respecta al artículo, cada participante del proyecto ha escrito las secciones correspondientes a su desarrollo, mientras que el planteamiento general y la escritura del conjunto del artículo han sido realizadas por David Cuesta de la UPV. Esperemos que su publicación contribuya a una mayor difusión del sistema desarrollado. Además, de cara a nuestro grupo, puede servir de ejemplo de que el trabajo de desarrollo e innovación puede y debe publicarse tanto como el de investigación.